Introduction
Security-as-a-Service (SECaaS) delivers cybersecurity solutions through cloud-based infrastructure on a subscription basis, enabling organizations to outsource security functions to specialized third-party providers. Unlike traditional on-premises security solutions that require significant capital investment in hardware, software licenses, and dedicated security teams, SECaaS shifts these responsibilities to a service provider, emphasizing outsourced security by entrusting the management of security infrastructure, continuous monitoring, and incident response remotely.
This article provides a comprehensive overview of SECaaS for IT professionals, managed security service providers, and enterprise security buyers evaluating cloud-based security solutions. The content covers service delivery models, types of SECaaS offerings, implementation considerations, and provider selection criteria. Topics outside this scope include specific vendor product comparisons and detailed technical deployment guides.
Direct Answer: SECaaS outsources cybersecurity functions to cloud-based providers who manage security infrastructure, threat detection, and incident response on a subscription basis, eliminating the need for in-house security staff and capital-intensive security tools.
After reading this article, you will understand:
- How SECaaS differs from traditional security and managed security service provider models
- The core components and cloud-native security delivery mechanisms
- Major categories of SECaaS solutions including identity and access management, threat detection, and data protection
- Cost-benefit analysis and operational advantages of subscription-based security services
- Vendor selection criteria and implementation best practices
Understanding Security-as-a-Service Fundamentals
Security-as-a-Service represents a cloud computing delivery model where security capabilities are provided by a third-party provider rather than deployed and managed internally. This approach emerged around 2001 as enterprises began adopting internet-based security services such as managed email security, anti-spam filtering, and antivirus protection. The model has matured significantly alongside cloud computing adoption, multicloud architectures, and the shift toward remote work environments.
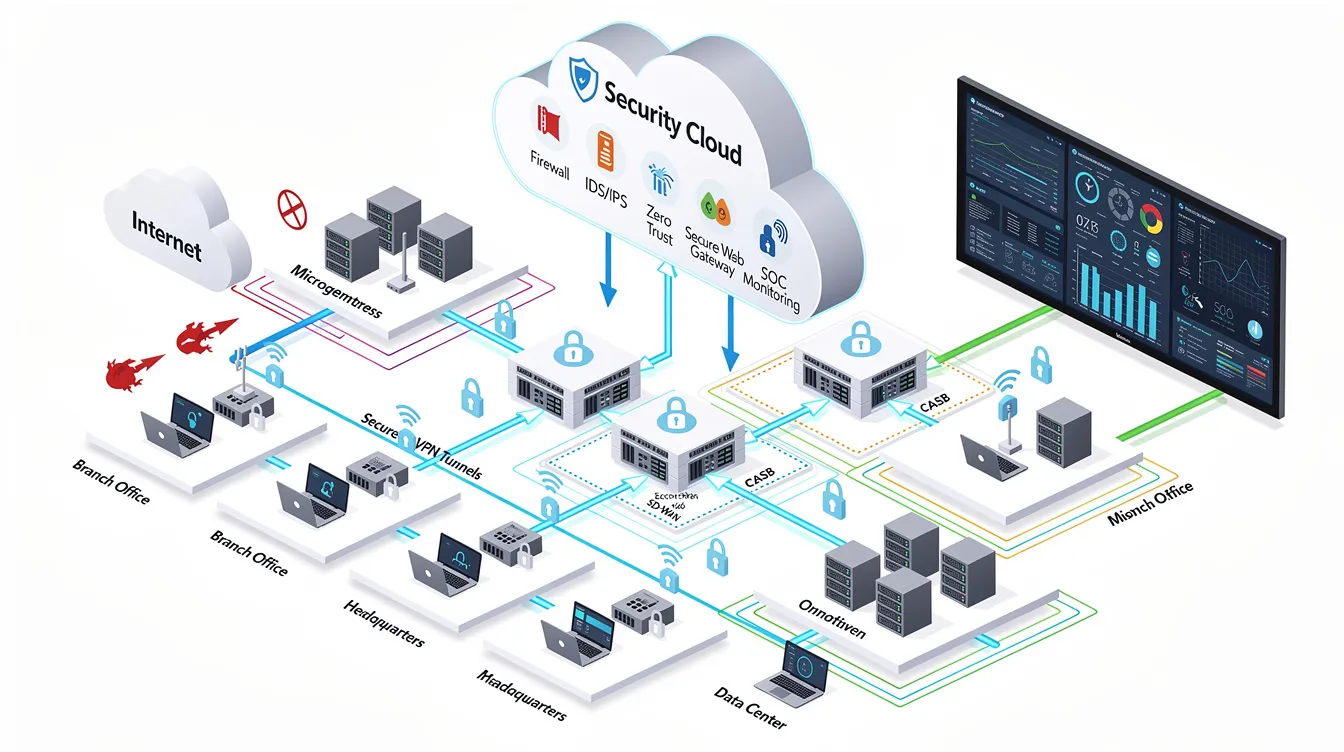
Modern enterprise security environments span hybrid cloud infrastructure, edge computing, mobile devices, and transient workloads including containers and serverless functions. Traditional network security tools, built on the foundation of enterprise networking, struggle with the scale, agility, and maintenance demands of these distributed environments. SECaaS addresses these limitations by providing security operations through elastic, globally distributed infrastructure with continuous updates and shared threat intelligence.
Core SECaaS Components
SECaaS solutions consist of three fundamental components that work together to deliver comprehensive security:
Cloud-Based Security Infrastructure: The SECaaS provider maintains the network infrastructure, servers, analytics platforms, and storage required for security operations. This infrastructure supports tools for security event management, endpoint protection, access management, data encryption, and data loss prevention.
Managed Security Operations: SECaaS providers deliver 24/7 security monitoring, threat detection and response, vulnerability management, security management, and security assessment services. These operations typically include human security analysts, alert management systems, and forensic capabilities. SECaaS vendors leverage automated AI analytics and dedicated 24/7 Security Operations Centers (SOC) to minimize the mean time to respond (MTTR).
Subscription-Based Consumption Model: Organizations pay recurring fees based on scope—number of endpoints, data volume, or service tiers—rather than investing capital in hardware and software licenses. Updates, maintenance, and threat intelligence are included in the subscription, eliminating the overhead of patching and upgrade cycles.
These components address traditional security limitations by reducing upfront capital costs, providing instant access to expert security talent, and enabling rapid scaling across cloud environments and geographic boundaries.
Cloud-Native Security Delivery
Cloud-native security architecture enables SECaaS providers to operate across elastic, dynamic environments. Key architectural principles include:
- Least privilege access controls that limit user and system permissions to minimum necessary levels
- Zero-trust security frameworks that verify every access request regardless of network location
- Automation and CI/CD integration for continuous security validation
- Immutable infrastructure that reduces configuration drift and vulnerability exposure
SECaaS providers aggregate threat intelligence across their customer base, enabling detection models that use machine learning to identify emerging threats. Real-time analytics, central log aggregation, and behavioral detection capabilities provide comprehensive protection for cloud environments, including their infrastructure and operating systems, that individual organizations would struggle to achieve independently.
Types of SECaaS Solutions
SECaaS encompasses multiple service categories that address different security functions, such as web security, email security, identity and access management, intrusion detection, and vulnerability scanning. Providers often bundle multiple services, but understanding each category helps organizations identify specific security capabilities they need.
Identity and Access Management as a Service
Identity and Access Management (IAM) provides control over who can interact with a network and the specific areas and applications they can access. Cloud-based IAM services include single sign-on (SSO), multi-factor authentication (MFA), privileged access management (PAM), and identity governance. These services enforce least privilege principles and protect against credential compromise by implementing conditional access policies based on user context, device posture, and risk signals. IAM as a service integrates with cloud environments and on-premises systems to provide unified access management across hybrid infrastructure.
Threat Detection and Response Services
Threat detection and response represents one of the fastest-growing SECaaS categories. Key service types include:
Managed Detection and Response (MDR): Providers monitor endpoints, network traffic, and user behavior to detect threats, with response capabilities ranging from automated incident response to coordinated remediation with customer security teams. AI-driven analysis and automated playbooks reduce threat response times from hours to minutes in SECaaS. Intrusion detection is a critical function within MDR, enabling continuous monitoring and identification of malicious activities such as unauthorized access and hijacking.
SIEM-as-a-Service: Security event management delivered as a service includes log collection, correlation, dashboards, alerting, and forensic capabilities without requiring organizations to deploy and maintain on-premises SIEM infrastructure. Intrusion detection systems (IDS) are often integrated alongside SIEM and endpoint security as fundamental components of a robust security infrastructure, providing essential capabilities for detecting and preventing unauthorized access.
Endpoint Security: Cloud-delivered endpoint protection platforms provide antivirus, anti-malware, and behavioral analysis across workstations, servers, and mobile devices with centralized management and continuous monitoring.
A critical factor in selecting a SECaaS provider is their response times to incidents, including mean time to detect (MTTD) and mean time to respond (MTTR). Intrusion management involves identifying potential intruders and addressing any discovered threats, often evaluated using these performance metrics to ensure timely detection and response.
Data Protection and Compliance Services
Data protection services address the security of information throughout its lifecycle:
Data Loss Prevention: Data loss prevention tools are designed to monitor, protect, and ensure the security of data both in storage and in use. These tools implement content inspection and exfiltration controls to prevent unauthorized data transfers.
Data Encryption: Encryption ensures that stolen data is rendered unreadable and useless without the encryption key, protecting sensitive information from unauthorized access. SECaaS providers offer encryption services for data in transit and at rest, along with key management capabilities.
Disaster Recovery and Business Continuity: Cloud-based backup and recovery services provide geo-redundant data protection and rapid restoration capabilities to maintain business operations following security incidents or system failures.
Compliance Support: SECaaS providers deliver regulatory compliance reporting, audit logs, and policy alignment services for frameworks including GDPR, HIPAA, PCI DSS, and SOC 2.
Common services provided by SECaaS include data loss prevention, continuous monitoring, disaster recovery, identity and access management, email security, and vulnerability scanning.

Benefits and Service Delivery Models
Understanding the operational and financial advantages of SECaaS helps organizations evaluate whether this model aligns with their security requirements, existing security environment, and business objectives.
Cost and Operational Benefits
Organizations should consider SECaaS when they lack internal security expertise, need to scale security capabilities rapidly, or want to reduce capital expenditure on security infrastructure. Key benefits include:
- Reduced Capital Expenditure: SECaaS eliminates the need to purchase premium hardware appliances, expensive software licenses, and infrastructure maintenance. According to a study by the Institute of Electrical and Electronics Engineers, SECaaS solutions often provide better cost savings and ease of management compared to traditional on-premises security solutions.
- Access to Expert Security Talent: SECaaS providers maintain full security operations centers, threat intelligence teams, and specialist security analysts. The SECaaS model allows organizations to access the latest security tools and expertise without the need for in-house security staff, making it suitable for businesses of all sizes. When choosing a SECaaS provider, organizations should evaluate the provider’s expert team, ensuring they have relevant certifications and experience in cybersecurity.
- Faster Deployment and Scaling: SECaaS services can be deployed in hours or days rather than weeks or months. SECaaS offers significant scalability, allowing organizations to quickly adapt their security solutions to meet changing business needs and emerging threats without the delays associated with traditional security implementations. It is essential to assess the scalability of a SECaaS provider, ensuring they can adapt their services to meet changing business needs and security threats.
- Automatic Updates and Threat Intelligence: SECaaS providers upgrade systems, deploy the latest threat signatures, and patch security vulnerabilities across their customer base. Distributed threat intelligence provides insights into emerging threats that individual organizations could not obtain independently. Organizations should check that their SECaaS provider offers 24/7 security coverage to ensure continuous protection against evolving threats.
Outsourcing log collection, system configuration, and continuous infrastructure auditing frees up in-house IT specialists to focus on core business strategies. SECaaS allows organizations to focus on their core business activities by outsourcing their security needs, which can lead to increased efficiency and productivity.
SECaaS vs Traditional Security vs MSSP Comparison
| Criterion | Traditional Security | MSSP | SECaaS |
|---|---|---|---|
| Deployment Model | On-premises hardware and software; internal security team management | Managed services for specific security functions; customer retains tool ownership | Cloud-hosted infrastructure; full-stack security delivered as service |
| Cost Structure | High CAPEX for hardware, software, and staffing; predictable but front-loaded | Lower CAPEX with recurring fees; incremental costs per service | Subscription-based; flexible scaling; bundled outcomes |
| Expertise Requirements | Requires hiring and retaining specialized security staff | External expertise for monitoring; customer handles response | Provider covers full spectrum including threat intelligence and incident response |
| Scalability | Limited by hardware capacity and staff availability | Moderate; dependent on provider capabilities | High; designed for multi-tenant scale and elastic usage |
| Control Level | Maximum control over configuration and data | Some control retained; reduced visibility into provider operations | Trade-offs between convenience and direct control; reliance on provider compliance |
| Response Capability | Internal processes; limited by staffing | Monitoring with alerts; customer typically handles remediation | Rapid response included in SLAs; automated or provider-led remediation |
Traditional networks rely on backhauling remote device connections back to a central data center via VPNs, creating severe bottlenecks. SECaaS addresses this limitation through cloud-native delivery that provides security services at the edge.
Organizations with limited internal security operations centers benefit most from SECaaS, particularly when they need outcome-driven security rather than tool ownership. Managed security service providers fit organizations that want managed operations while retaining more control over security tools and configurations.
Common Use Cases and Implementation Considerations
Practical applications of SECaaS span multiple enterprise scenarios, but successful implementation requires understanding potential security challenges, addressing these obstacles proactively, and establishing clear provider selection criteria.
Enterprise Use Cases
Cloud Migration Security: Organizations moving applications and data to public cloud environments use SECaaS to enforce consistent security policies, protect cloud workloads, and monitor for misconfigurations across cloud environments. During migration, organizations collaborate with SECaaS vendors to develop security measures that address risks and ensure a secure transition. Cloud workload protection services provide visibility into container, serverless, and virtual machine security posture.
Remote Workforce Protection: Securing distributed endpoints and remote access to corporate resources requires identity and access management, multi-factor authentication, and zero-trust network access. SECaaS providers deliver these capabilities without requiring VPN infrastructure or on-premises security appliances.
Compliance Management: Organizations in regulated industries—healthcare, financial services, government—rely on SECaaS for maintaining audit logs, compliance reporting, and security controls aligned with regulatory requirements. SECaaS providers typically deliver a range of services including threat detection, incident response, and data loss prevention, allowing organizations to focus on core business activities.
Incident Response Preparedness: Organizations without internal incident response capabilities use SECaaS to ensure rapid threat detection and response through contractual SLAs. SECaaS offers affordable, scalable protection against threats like malware, ransomware, and data breaches.
Implementation Challenges
Vendor Dependency: One of the challenges of SECaaS is the dependency on the service provider for security, which can lead to concerns about data privacy, security issues such as vulnerabilities in the provider’s systems, and the security of the service itself. Relying on a single SECaaS vendor can create challenges if service level agreements prove inadequate, pricing escalates, or proprietary technology limits portability.
Integration Complexity: SECaaS tools must integrate with existing identity providers, logging systems, cloud providers, APIs, and on-premises infrastructure. Misalignment or lack of compatibility can reduce security effectiveness and create visibility gaps.
Data Sovereignty Issues: Laws in many jurisdictions mandate that certain data categories must reside in specific geographies or prohibit cross-border data transfers. SECaaS providers based in different jurisdictions may introduce legal and compliance risks.
Performance Considerations: Delivering security services over cloud infrastructure involves network latency, dependency on internet connectivity, and potential service outages. Real-time threat detection requires low-latency connections to security analytics platforms.
Gartner predicts that by 2025, 99% of cloud security failures will be the fault of the customer rather than the service provider, highlighting the importance of proper implementation and management of SECaaS solutions.
Provider Selection Criteria
When evaluating SECaaS providers, organizations should assess:
Security Certifications: Verify ISO/IEC 27001, SOC 2, PCI DSS, HIPAA, or other certifications relevant to your industry and compliance requirements.
Service Level Agreements: Evaluate defined response metrics including mean time to detect (MTTD), mean time to respond (MTTR), escalation paths, and threat coverage guarantees.
Integration Capabilities: Assess ability to integrate with existing identity platforms, cloud providers, and security tools. Verify support for APIs, agents, and common security data formats.
Compliance and Data Residency: Understand where data resides, how the provider handles cross-border data flows, legal jurisdiction, data encryption practices, and key management procedures.
Vulnerability Scanning: Vulnerability scanning examines IT infrastructure and networks for entry points or vulnerabilities that could be exploited by cyber criminals. Ensure the provider includes comprehensive vulnerability management and penetration testing capabilities.
The top SECaaS providers include a mix of specialized firms and large cybersecurity companies, each offering unique strengths such as advanced threat intelligence and cloud security solutions.
Conclusion and Next Steps
Security-as-a-Service provides a cloud-delivered security model that reduces capital expenditure and operational complexity while improving threat protection capabilities. Organizations gain access to expert security teams, advanced security technologies, and continuous monitoring without building and maintaining internal security operations centers. SECaaS allows organizations to scale their security solutions up or down as needed, providing flexibility to adapt to changing business priorities and emerging threats.
To evaluate and implement SECaaS effectively:
- Assess current security gaps and requirements: Identify critical assets, threat models, regulatory compliance obligations, and existing security capabilities that need augmentation
- Define desired security outcomes: Specify metrics such as reduced response time, zero-trust implementation, or specific compliance certifications
- Evaluate SECaaS providers against selection criteria: Compare certifications, SLAs, integration capabilities, and data residency options
- Plan pilot implementation for non-critical systems: Validate performance, integration, and operational workflows before full deployment
- Develop integration and migration strategy: Address data migration, agent deployment, policy harmonization, and oversight procedures
Related topics for further exploration include cloud security architecture principles, zero-trust implementation frameworks, security automation strategies, and managed security services comparison methodologies.
Frequently Asked Questions
What is Security-as-a-Service (SECaaS)?
SECaaS is a cloud computing model where security capabilities are delivered by a third-party provider on a subscription basis. SECaaS providers offer a subscription model for delivering cybersecurity solutions through the cloud, allowing organizations to access a range of key cybersecurity services without the need for in-house management. Services typically include threat detection, incident response, identity and access management, and data loss prevention.
How much does SECaaS cost?
SECaaS pricing follows subscription or pay-per-use models based on number of users, endpoints, data volume, or service tiers. This approach converts capital expenditure to operational expenditure, with costs varying significantly based on service scope and provider. Review financial commitments carefully to understand total cost of ownership compared to traditional alternatives.
How long does SECaaS implementation take?
Implementation timelines vary by service complexity. Basic services such as email security or endpoint protection can deploy within days. Full security operations center deployment including log ingestion, integration, and custom policies may require several weeks to months.
How effective is SECaaS at preventing cyber threats?
When properly implemented, SECaaS provides highly effective security through continuous monitoring, expert security analysts, and aggregated threat intelligence. AI-driven analysis and automated playbooks reduce threat response times from hours to minutes. However, effectiveness depends on provider quality, integration completeness, and adherence to security best practices.
Does SECaaS support regulatory compliance requirements?
SECaaS providers typically offer compliance documentation, certifications (ISO, SOC 2, PCI DSS, HIPAA), audit logs, encryption, and data retention aligned with major regulations. Organizations must verify that specific providers meet their regulatory requirements and data residency obligations.
What is vendor lock-in risk with SECaaS?
Vendor lock-in concerns arise when providers use proprietary agents, data formats, or technologies that limit portability. Mitigation strategies include clear contract terms, data export rights, selection of interoperable tools, and gradual pilot programs before full commitment.
What are data sovereignty risks with SECaaS?
Data stored or processed in foreign jurisdictions may be subject to laws such as the US CLOUD Act, potentially conflicting with obligations under GDPR or other privacy regulations. Evaluate provider data residency options and ensure alignment with jurisdictional requirements.
How does SECaaS differ from MSSP services?
Managed security service providers typically monitor and alert on security events but expect customers to handle remediation. SECaaS often includes response and remediation capabilities as part of the service, providing more outcome-oriented security operations. SECaaS represents a more tightly integrated, full-stack security service compared to traditional MSSP models.
What integration requirements does SECaaS have?
SECaaS providers typically require agents or APIs to collect logs and endpoint telemetry, access to identity systems, cloud provider permissions, and potentially network flow data. Organizations need consistent identity infrastructure and clear data sharing agreements to enable effective integration.
Can small businesses use SECaaS?
SECaaS is particularly well-suited for small and medium businesses that lack resources to build internal security teams. The subscription model provides access to enterprise-grade security capabilities without significant capital investment or specialized hiring requirements.

